DataVault, Irc Warez (Ty 4 Moving X).txt 2.7 KB
-[ How to rip Dynamic Flash Template ]-.txt 2.2 KB
10 reasons why PCs crash U must Know.txt 12.2 KB
10 Security Enhancements.txt 2.7 KB
16x Dvd+-rw Dl Dvd Writer Comparison Guide.txt 6.1 KB
20 Great Google Secrets.txt 8.8 KB
23 Ways To Speed WinXP, Not only Defrag.txt 10.1 KB
250+ Tech books online.txt 23.3 KB
36 Graphics & Design Ebooks.txt 3.6 KB
8 People Can Use The Same Msn Dial Up Account.txt 1.3 KB
A Basic Guide to the Internet.txt 12.4 KB
A very small tut for RealMedia.txt 644 Bytes
A Web Standards Checklist, How to make a proper website.txt 18.9 KB
Accessing The Entire Internet On Your 3 Phone, U8110, E616 etc..txt 1.2 KB
Advanced Shellcoding Techniques.txt 7.4 KB
All about ftp must read.txt 19.5 KB
All About Movie Tags (what Is A Dvdrip, Cam Etc.).txt 17.3 KB
ALL About Spyware.txt 6.1 KB
All mIRC Commands.txt 6.6 KB
Anonymity of Proxy, Anonymity Of Proxy learn it insideout.txt 4.9 KB
Anonymity.txt 12.8 KB
anti leech hacking tutorial.txt 1013 Bytes
Auto End Tasks to Enable a Proper Shutdown, Win XP Tweak.txt 821 Bytes
Automatic Windows Installation, No keypress required!.txt 275 Bytes
B.A. regedit.txt 1 KB
Backtracking EMAIL Messages.txt 5.8 KB
Bandwidth Explained!.txt 7.8 KB
Beep Code Manual.txt 6.5 KB
Beep Codes Error Codes.txt 3.5 KB
Best Keyboard Shortcuts.txt 8.1 KB
Big Brother And Ndisuio.sys, A new Internet phenomenon.txt 1.8 KB
Bin & Cue Simple Tut.txt 2.3 KB
BIOS Update Procedure.txt 5.4 KB
Bit Torrent Tutorials.txt 5 KB
Block Adservers.txt 48.4 KB
Boot Block Recovery For Free.txt 6.5 KB
Boot Winxp Fast.txt 948 Bytes
Border And Text Effects In Psp8, For use with PSP8.txt 3.2 KB
Broken Ie, How to fix it.txt 1.2 KB
Bulk Editing Of .xxx to .zip or .mp3.txt 962 Bytes
BulletProof FTP Server Tutorial.txt 4.3 KB
Burn .bin file Without A .cue file.txt 1.3 KB
Burn a BIN without a CUE using NERO.txt 1.1 KB
Burning Bin & Cue Using Nero.txt 2.3 KB
Bypass Internet Censorship.txt 229 Bytes
Calculating Offsets.txt 5 KB
cannot use my password to get back into Windows XP.txt 2.1 KB
Cant See Secure Sites.txt 658 Bytes
Caught A Virus.txt 8.3 KB
Change Music In The Malibu And The Pole Position, GTA Vice Modders.txt 838 Bytes
Change Text on XP Start Button.rtf 3.4 KB
Change Text on XP Start Button.txt 3 KB
Change The Default Location For Installing Apps.txt 654 Bytes
Change The Storage Location Of 'my Documents', a bit safer for when your PC crashes....txt 661 Bytes
Change Your Ip In Less Then 1 Minute.txt 1.6 KB
Changing Default Location For Installing Apps.txt 805 Bytes
Check For Dos, Check to see if you are infected..txt 6.4 KB
Choosing A Good Domain Name, ya..good name is important!.txt 6.3 KB
Choosing An Internet Merchant Account, nice info on Internet Merchant Account...txt 6.1 KB
Clear Unwanted Items From Add And Remove.txt 212 Bytes
Closing Open Holes, System Security How to close open holes.txt 18.6 KB
CMD Prompt here, add to folder context menu windows xp.txt 711 Bytes
COMMON FTP ERROR CODES.txt 2.4 KB
Computer Acronyms.txt 9.6 KB
Computer Matinence.txt 3.1 KB
Configuring ZoneAlarm Pro Security Settings, A ZoneAlarm Pro Tutorial.txt 2.1 KB
connect A Psx Pad To Pc, Warning soldering is involved...txt 2.4 KB
Convert Stubborn Webpage To pdf.txt 701 Bytes
Convert To Basic And Dynamic Disks In Windows Xp.txt 4 KB
Converting Movies To Psp Format.txt 2.6 KB
Converting to NTFS.txt 4.8 KB
COPY X BOX GAMES!.txt 1.1 KB
Cracking Bios, use the followin' code.txt 890 Bytes
Cracking Zip Password Files.txt 9 KB
Crap Software Config Settings, How to set-up the firewall.txt 3.6 KB
Create A Huge File.txt 1.1 KB
Create A Personal Screen Saver In Win Xp!.txt 640 Bytes
Create An Ftp Server On Your Pc With Serv-u.txt 4.6 KB
Create Bootable Win XP SP1 CD(nero).txt 2.2 KB
Create Bootable XP SP integrated CD.txt 3.8 KB
Create One-click Shutdown And Reboot Shortcuts.txt 1.4 KB
Creating a Board aka Forum on your own PC !.rtf 912 Bytes
Creating Universal Ghost Usb Boot Disk And Cd.txt 1.9 KB
Data Capacity of CDs [Tutorial].txt 6.6 KB
Debug, Learn how crack windows.txt 9.5 KB
Delete An undeletable File.txt 2 KB
Delete Files From The Recent File List In Windows.txt 1.4 KB
Digital Camera Guide.txt 5.9 KB
Digital Faq -learn Everything About Digital, Capture, Edit and Burning and more.txt 2.2 KB
Digital Photo Id Cards, Greate Info.txt 2.9 KB
Direct Link To Any Page You Want To In Hotmail.txt 1.9 KB
Directx Explained.txt 7.7 KB
Disable Compression On Xp, NTFS partition, Disk Cleanup.txt 440 Bytes
Disable The Send Error Report, to Microsoft.txt 520 Bytes
Disable Windows Logo Key.txt 636 Bytes
Discover New Music You'll Probably Love.txt 1.1 KB
Do You Want To Learn Maya 6, look, some tutorials.txt 76 Bytes
Doom 3 Speed Up, Guaranteed 40% better.txt 1.5 KB
Doom3 Simple Tweeks, how to run doom with tweeks.txt 5.9 KB
Dos User - No Boot Dos Disk, No Edit.com,How to create Imp Files.txt 691 Bytes
Download Free Music legally,, legally.txt 3.2 KB
Download from a paypal site without paying a penny!.txt 971 Bytes
Download From Ftpz, Using Ftp Search Sitez.txt 8.1 KB
Download Mp3's Without Using Filesharing.txt 711 Bytes
Download Music And Video With ,edia Player9, quick and easy!.txt 678 Bytes
Download Timeframes.txt 339 Bytes
Downloading Files, Using Archives And Images.txt 8.4 KB
Downloading Windows Media Streams.txt 751 Bytes
Dreamweaver Tut That Teaches U, to search a database with phpmysql.txt 2.2 KB
Driverguide.com.txt 1.4 KB
Dual Boot After The Fact.txt 1.4 KB
Dvd Copying-ripping Definitions.txt 1.3 KB
DVD Regions Information.txt 3.8 KB
Dvd-9 to Dvd+r Dl, Double Layer To Double Layer, 1-1 copies.txt 967 Bytes
Easily Disconnect-reconnect From Broadband.txt 309 Bytes
Easily Find Serial Numbers On Google.., easy to do and works like a charm..txt 1.4 KB
Ebay Hackcracktip.txt 513 Bytes
Eliminate Ie's Autocomplete Reminder.txt 1.2 KB
Email Forge, sends email from anyone.txt 1.4 KB
Enable Folder and Icon Refresh, Win XP Tweak.txt 564 Bytes
Erasing_Your_Presence_From_System_Logs.txt 2.6 KB
Evolution Of Computer Viruses History Of Viruses.txt 20.6 KB
Excellent tricks and techniques of Google Hacks.txt 157.7 KB
Exploseek, a simple tool to find music on the net.txt 650 Bytes
Find Stuff.txt 1020 Bytes
Finding Missing Files From A Release.txt 1 KB
Firefox Speed Tweaks.txt 1.5 KB
Firefox Tweaks.txt 305 Bytes
FlashFXP FAQ.txt 4.6 KB
Flashget Broadband Tweak.txt 639 Bytes
FLASHGET INTEGRATION IN OPERA,MOZILLA,NETSCAPE.txt 3.9 KB
FlashGet v1.4 - More Download Simultaneously.txt 1.2 KB
Flashing A Video Card Bios [advanced Guide], Step-by-Step Guide for Novice and Expert.txt 1.3 KB
Formatting An Hdd, when fdisk won't.txt 1.3 KB
Free Access To Websites Without Registering.txt 779 Bytes
FREE Hosting For WAREZ.txt 2.2 KB
FREE Hosting List php, mysql and more.txt 20.8 KB
Free World Dialup.txt 3.6 KB
Free X-box Live !.txt 721 Bytes
Freebsd Install Guide.txt 11.9 KB
General Keyboard Shortcuts, General Keyboard Shortcuts.txt 7.5 KB
Get In Windows 2000 As Administrator.txt 399 Bytes
Get the Most Out of Your DVD Recorder.txt 11.2 KB
Get The Music You Want To Hear.txt 920 Bytes
Get unlimited bandwidth from your host for free.txt 2.9 KB
Getting A 1gb Yahoo China Account.txt 1000 Bytes
Getting Counter-strike Source To Work.txt 3.4 KB
getting movies, mp3,games using google.txt 765 Bytes
Getting older programs to run on Windows XP.txt 3 KB
Getting started with Linux for nOObs!.txt 17.4 KB
Go to Windows updates anonymously.txt 410 Bytes
Google Crack Search.txt 140 Bytes
Google secrets.txt 1001 Bytes
Google Tips & Tricks, (utilizing search engine).txt 5.8 KB
Graffiti On Walls 4 Adobe Photoshop Cs 8.0.txt 2.4 KB
Guide For Getting Free Stuff.txt 10.3 KB
Guide to IIS Exploitation.txt 27.8 KB
Guide to Slipstreaming Service Pack 2.txt 2.8 KB
Hard drive Gone Bad.txt 5.6 KB
Hardware Firewall.txt 3 KB
Have Notepad In Send To.txt 1.9 KB
have satallite tv for almost free IF not free!!!.txt 3 KB
Hex, How to turn binary or decimal to hex.txt 1022 Bytes
Hide Drives and Partitions.txt 2.4 KB
How 2 Find EVERYTHING uploaded on Rapidshare.txt 449 Bytes
How do I overburn a CD with Nero.txt 861 Bytes
How do I remove an extra operating system from by.txt 685 Bytes
How do I Test My VirusScan Installation.txt 1.7 KB
How Do U See Hidden Files, Using DOS...txt 149 Bytes
How Download MP3s from Fanscape.com or other Streaming Audio-Video.txt 2.4 KB
How Linux boots.txt 13.2 KB
How Long Has Your XP System Been Running.txt 551 Bytes
How To Access Your Folders From Your Taskbar.txt 1 KB
How To Add A Url Address Bar To The Taskbar.txt 845 Bytes
How To Add An Option To Print, the Contents of a Folder!.txt 1.5 KB
How To Add Your Own Windows Tips.txt 488 Bytes
How to Back Up the Registry.txt 775 Bytes
How To Backup Ps2 Games.txt 7.7 KB
HOW TO BLOCK PEOPLE ON WINMX WHO SHARE NOTHING.txt 1.5 KB
How To Block Websties Without Software, block websites.txt 652 Bytes
How To Boot Xp Faster (updated).txt 1.7 KB
How to build a black box.txt 7.8 KB
how to burn quicker in windows xp.txt 290 Bytes
How to Bypass BIOS Passwords.txt 9 KB
How To Bypass Web Filters, tutorial.txt 6.2 KB
HOW TO CAPTURE STREAMING MEDIA.txt 1.7 KB
How To Change A Cmos Battery.txt 3.2 KB
How to change the serial number used in Windows XP, Valid for XP Corporate.txt 1.1 KB
How To Change Thumbnail Size And Quality.txt 925 Bytes
How to clear Bios info 2.txt 23.6 KB
How to clear Bios info.txt 11.7 KB
How To Convert File System, fat - fat32 to ntfs.txt 530 Bytes
How To Copy A Dvd Which Will Play On A X Box.txt 1 KB
How to copy songs from your iPod to your PC.txt 1.4 KB
How To Customise Your start Button.txt 1.5 KB
How To Delete Those Persistent Nasty Files.txt 539 Bytes
How To Directly Go To Inbox, Write Msg, w Hotmail, no need for hotmail today - http users.txt 1.5 KB
How To Disable Picture And Fax Viewer.txt 784 Bytes
How to do a high Quality DivX rip.txt 5.6 KB
How To Download Bittorrent Files.txt 7.1 KB
How To Download Directly From Crackdb.com.txt 1.7 KB
How To Download Movies, From IRC.txt 20.2 KB
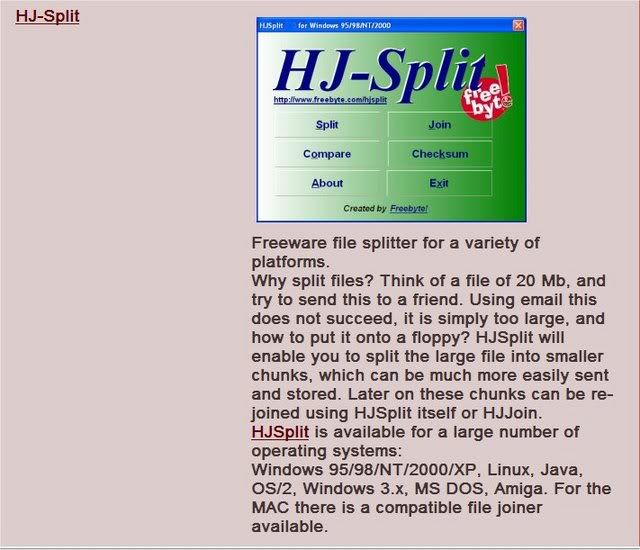
How to Download-Upload Files from email.txt 23.1 KB
how to edit right click menu.rtf 4.6 KB
how to execute chm files in linux.txt 673 Bytes
How to Extend the life of the yousendit download links.txt 613 Bytes
How to find a remote IP.txt 1.9 KB
How To Find Ftp's The Easy Way'.txt 588 Bytes
How to find MP3's real quickly.txt 359 Bytes
How To Find Serial Numbers On Google.txt 812 Bytes
How to fix corrupted files in XP.txt 1.5 KB
How to fix Windows Installer problem.txt 981 Bytes
How To Get A Free I-pod Or Flat Screen Tv, check it out.txt 6.6 KB
HOW TO GET ANY WINDOWS PASSWORD.txt 3.4 KB
How to Get someones ISP password, Get free internet.txt 2.7 KB
How To Get Top Ranking, Search Engines.txt 6.6 KB
How To
Hack Windows Xp Admin Passwords.txt 2.5 KB
How to hack-change your Windows XP Boot Screen.txt 1.5 KB
how To Hide Yourself From Network Users!, And give access to only specific users!.txt 883 Bytes
How To Increase Download Speeds By 100-200 Kbsec.txt 319 Bytes
How to Install and run Windows CE on your USB Stick.txt 1.1 KB
How To Make 5cds, 10cds Or 2dvds From Official Dow, These are same as Mandrake PowerPack+.txt 3.4 KB
How To Make A Kvcd.txt 6 KB
how to make a new web site.txt 927 Bytes
How To Make A Transparent Background, .fla .swf.txt 108 Bytes
how to make a VCD from a DivX.txt 7.4 KB
How To Make An Animted Logo.txt 5.3 KB
How To Make Free Phone Calls.txt 2.3 KB
How to make key generators.txt 8.8 KB
How To Make Perfect Copies Of Maxis The Sims Discs, CloneCD Style!.txt 1.2 KB
How To Make XP Go Faster.txt 5.6 KB
How To make your own Radio Station 2.txt 3.3 KB
How To Make Your Own Radio Station.txt 1.6 KB
How To Make Your Own Radiostation.txt 1.6 KB
HOW TO MANUAL - THE END OF DELETERS.txt 12.9 KB
How to modify exe files.txt 2.5 KB
How To Move Xp Harddrive To New Motherboard.txt 887 Bytes
How To optimize DSL-CABLE connection speed.txt 382 Bytes
How To Play Movies (divx Etc) With Subs.txt 1.4 KB
How to recover MOST of scratched CD data discs.txt 2.7 KB
How to Remove DRM Protection for Video Files.txt 2.3 KB
How To Remove Ms Java Vm And Install Sun Java.txt 51 Bytes
How To Remove Signin Details Of Msn Passport.txt 1 KB
How To Remove The Default Admin$ Shares.txt 1 KB
How to remove the Links folder in IE Favorites.txt 604 Bytes
How to Remove WinXP Splash and See Operations.txt 1.2 KB
How To Rename Extensions With Ease, with a Renamer.bat file!.txt 452 Bytes
How to Rename File Extensions.txt 3.1 KB
How To Rename Multiple Files In Winxp.txt 571 Bytes
How To Restrict Login Hours Allowed.txt 599 Bytes
How to safeguard your files when computer crashes.txt 2.9 KB
How to save Windows xp updates.txt 646 Bytes
how to search google for RAPIDSHARE links.txt 1004 Bytes
How To See Hidden Files, Using Dos.txt 86 Bytes
How To Set search For All Files In Winxp.txt 731 Bytes
How to set up a http server running from you computer.txt 3.1 KB
How To Set Up A Proxy In Flashget, As Requested.txt 672 Bytes
How to set up a server with Apache , PHP , MySQL , Perl , phpMyAdmin.txt 8.8 KB
How To Set Up Direct Connect.txt 27 KB
HOW TO SET UP FTP SERVER.txt 1.8 KB
How To Set Up Proxies In Your Browser.txt 1.6 KB
How To Set Zone Alarm Settings!, Fix for ZA ports.txt 2.1 KB
How To Setup Your Own Dns (Domain Name Server).txt 7 KB
How To Speed Up A Slow Computer.txt 1.2 KB
How To Speed Up Http Requests On Internet Explorer, as above.txt 1.3 KB
How To Stop Spam.txt 8 KB
How to swear in all languages.txt 28.3 KB
How To Unload Cached Dll Files To Free Memory.txt 572 Bytes
How to Use and How to Chain Multiple Proxies!.txt 9.7 KB
How To Use File Compression In Windows Xp.txt 4.2 KB
How To Use Google To Download Mp3's, and applications.....txt 615 Bytes
How To Use Newsgroups.txt 573 Bytes
How To Use You Gmail With Msn Messenger.txt 379 Bytes
How-to Get Videos And Dvds Onto Your Sony PlayStation Portable (PSP) for free.txt 12.9 KB
HOWTO Change Windows XP Home to Windows XP Pro.txt 1.7 KB
Important Faqs For Sp2.txt 9.5 KB
Improve Doom 3's Performances!!, simple but efficient trick for every1.txt 4.2 KB
Improve your dialup modem preformance.txt 743 Bytes
Increase XP Folder Settings.txt 813 Bytes
Insert Your Serial For Office 2k, auto install office.txt 1.1 KB
Install A New Hard-disk.txt 5.2 KB
Install Xp From Dos.txt 862 Bytes
Installing Apache on Windows.txt 6.3 KB
Installing Gentoo Linux, Amazing step by step tutoria.txt 197 Bytes
Installing IIS On Windows Xp Pro.txt 3 KB
Installing Slackware Linux.txt 34.7 KB
Instructions For Removal Of Advertising In Msn Messenger.txt 2.6 KB
Ip Address Structure, Expilinatin OF IP Address {A short way}.txt 7.7 KB
Irc How To Downlaod From, How to downlaod from IRC.txt 4 KB
Irc Servers On nix, For people who want to start own IRC net.txt 489 Bytes
Keep Files Private.txt 1.5 KB
Keep Folders Hidden.txt 472 Bytes
Keyboard Shortcuts Result in Excel 2000 - Movement.txt 1.6 KB
Keyboard Shortcuts, Microsoft Word.txt 2.4 KB
Keyboard Shortcuts, must read.txt 3.7 KB
Kill Microsoft Instant Messenger.txt 287 Bytes
Lamination Tips, Its a Fast TUT......txt 2 KB
Leet Way To Get Your Ip In Windows Xp.txt 271 Bytes
Linking Your Xbox To Your Computer.txt 33.5 KB
Linux Howto's.txt 78 Bytes
List Of Sites Not To Go To.txt 4.3 KB
Little help for anonymous mailer.txt 1.6 KB
Lots Of Windows Xp Tips, Take A Look !.txt 12.4 KB
Lyrics With Google.txt 84 Bytes
Make A Autorun File For Ur Cd.txt 674 Bytes
Make A Batch File To Clean UR PC!!, All In One!!.txt 1.4 KB
Make A Roughly 16 Hour Video Dvd.txt 1 KB
Make Acrobat Reader 6 load faster.txt 427 Bytes
Make Dvd Iso From Suse 9.2 5 Cds Iso, Linux mode and Windows mode ISO creation.txt 7.4 KB
Make Mp3 Files Smaller Without Losing Quality.txt 744 Bytes
Make Your Own Ringtones For Mobile Phone, also logos, wallpaper, etc.txt 3 KB
Make Your Pc Faster, Guaranteed.txt 6.2 KB
MakeXPgoFaster.txt 5.7 KB
making a .cue file, in notepad.txt 544 Bytes
Making A .txt Executable Server.txt 1.6 KB
Making Bootable Floppy Disk to Boot into Windows.txt 4.8 KB
Making Cd Version Of Doom3 Into Dvd Version.txt 766 Bytes
Making Web Page Fonts Consistent and Uniform.txt 816 Bytes
Manage Saved Ie Passwords.txt 763 Bytes
Mastering The Windows XP Registry.txt 5.8 KB
Maximize Dial-up Modem Settings.txt 2.3 KB
Microsoft's Really Hidden Files, Reveled Hidden files.txt 34 KB
mIRC Not Just Another Chat Client, Download Anything You Want Almost.txt 4.4 KB
mIRCcommands.txt 10.1 KB
Misc Linux Tips & Tricks.txt 18.5 KB
Missing Administrator Account.txt 533 Bytes
Mobile Secret Codes.txt 31.1 KB
Modify .exe Files And Crack A Program.txt 3.1 KB
More Xp Tips and tricks make your computer more faster.txt 46.1 KB
Moving and Removing the Start Button.txt 680 Bytes
Msn Messenger & Gmail.txt 3.7 KB
My Flash Bookmarks, long list of tutorials.txt 3 KB
Myth about WPA ( How it is done ), Windows Product Activation Technique.txt
45.5 KB
Nero How To Verify The Validity Of The Sn U Use.txt 903 Bytes
New Pc Or New Motherboard.txt 3.8 KB
New Way To Relive Some Zinio File.txt 1.9 KB
news groups the how to do.txt 11.4 KB
Nice list of windows shortcuts.txt 7.5 KB
No Text Icons.txt 299 Bytes
Ntfs Cluster Size, better harddrive performance.txt 1.3 KB
Official Unattended Xp Cd Guide Xp Sp2 @ Msfn.org.txt 929 Bytes
Open Windows Explorer To A Different Default Direc.txt 754 Bytes
Optimize Broadband & Dsl Connections.txt 1.9 KB
Optimize Emule Connection.txt 1.2 KB
Outpost Rules, Outpost rules for system & app.txt 7.3 KB
Outsmarting System File Protection.txt 5.4 KB
Overclocking_Tutorial.txt 7.7 KB
Packet Attacks - Version 1.1, { Packet_Attack_Exlained}.txt 25.9 KB
Part 0 Dc++.txt 4.1 KB
Part 1 Bittorrents.txt 4.2 KB
Part 2 Irc (mirc).txt 4.9 KB
Part 3 Ftp.txt 2.7 KB
Partitioning Your Harddisk With Fdisk.txt 2.1 KB
Pc File Extention Listing.txt 26.5 KB
Pc Maintenance Guide.txt 10.2 KB
Peer2mail Tutorial.txt 9.4 KB
Performance Increase Through My Computer.txt 541 Bytes
Play Games On PS2 Without ModChip.txt 5.4 KB
Play On A Bnet Emulator, and f off cd key check =).txt 1.8 KB
Port Numbers.txt 40.2 KB
Problem With Internet Navigation, Clean Host File.txt 484 Bytes
Quick Fix For Spyware, Try This Before Doing Surgery on Your OS.txt 1.8 KB
Quick Msc.txt 513 Bytes
Quick Shutdown for XP, How to create a shutdown shortcut..txt 553 Bytes
Quickly Start The Shared Folder Wizard.txt 409 Bytes
Rapidshare
hack!!!!! Free premium acount for all.txt 3.1 KB
Rapidshare Hacked, unlimited upload, no countdown.txt 1.7 KB
Rapidshare Timelimit.txt 1001 Bytes
Read This! Av Compare!.txt 7.6 KB
Recover A Corrupted System File.txt 1.1 KB
Recover a Quick erased CD RW.txt 3.9 KB
Reformat&Reinstall.txt 2.6 KB
Regedit.exe & Regedt32.exe, Whats the difference.txt 2.9 KB
Registry Disassembled a basic tutorial.txt 7.1 KB
Reinstall Internet Explorer 6.txt 1.1 KB
Release Codes, Read, and Learn....txt 2.3 KB
Remote Desktop Through Company Firewall.txt 2.6 KB
Remote Shutdown.txt 1.2 KB
Remove Linux From Your Pc Safely, ...and restoring your MBR.txt 1.7 KB
Remove Msn Messenger From Xp, several ways...txt 5 KB
Removing Banners From Free Webhosts.txt 2.7 KB
Removing Norton Anti-virus 2004, How to remove the Registry Enteries.txt 995 Bytes
Rename 'recycle Bin' To Whatever You Want.txt 680 Bytes
Reregister All .dll Files Within Registry.txt 1.5 KB
Reset your lost Bios Password.txt 4.2 KB
Restore JPG,JPEG,JPE Default File associations, Win XP Tweak.txt 1.3 KB
REVERSE CODING.txt 15.1 KB
Run Aol Without Using Aol Browser & Save Resources, connect permanently and use any browser.txt 447 Bytes
Running A Board forum From Your Own Pc.txt 2.3 KB
Running Vanishing Console Programs With A Click!, Ever had a console program that vanis....txt 1.1 KB
Safely Editing the Registry....txt 1.9 KB
Save Your Desktop Icon Settings.txt 2.2 KB
Saving and loading Photoshop actions.txt 1.8 KB
Scheduled Tasks - Defrag, how to set up scheduled defrags.txt 1.9 KB
ScreenLock Professional v2.0.41.txt 43 Bytes
SEARCH eBOOK in FTP SEARCH ENGINE.txt 442 Bytes
Search For Ebook Server With Google.com.txt 362 Bytes
Search like a real warez d00dz, for warez of course!.txt 581 Bytes
Searching For Something To Download, This may help.txt 350 Bytes
Secret Backdoor To Many Websites.txt 2.1 KB
Secrets Of Lock Picking.txt 53.7 KB
Securing WinXP Pro (with what win-xp has to offer.txt 9.6 KB
Securing your WINDOWS XP computer.txt 1.2 KB
Set Google as your Default Search in IE.txt 561 Bytes
Set Win Explorer to open the folder you want!, Little trick.txt 234 Bytes
sick of inserting winxp cd every time your pc asks, Change Default Location of i386 Folder.txt 3.2 KB
sidebar fix.txt 587 Bytes
Simple Tweaks For Peak Pc Graphics Performance.txt 10.2 KB
Single Click Shutdown.txt 2.8 KB
Single-click To Open An Item..., IF the Folder Options is grayed out.txt 1.2 KB
Slow Loggon Time, one fix for problem.txt 986 Bytes
Slow Opening Of File Dialogs.txt 1.1 KB
Some Cool Site For Tutorials.txt 420 Bytes
Some Google Tricks, again.txt 1.7 KB
Some More Tips To Improve Your Winxp.txt 24.1 KB
Sp2 For Xp Slipstream, Integrate SP2 into your XP CD.txt 10.7 KB
Sp2 Tweaks.txt 3.4 KB
Speed Up Internet.txt 4.5 KB
Speed up menu display.txt 557 Bytes
Speed up Mozilla FireFox.txt 464 Bytes
Speed Up Your Bandwidth By 20% !, Windows uses 20% of your bandwidth.txt 1 KB
Speeding up menus in XP.txt 273 Bytes
Speeding up your internet connection under Linux and Windows.html 11.8 KB
Spoofing emails, via telenet.txt 417 Bytes
Standard ASCII Character Set.txt 1.8 KB
Steps to Clean Install XP.txt 8.2 KB
Stop A Restart Process In 3steps.txt 300 Bytes
Stop Annoying Pop-ups Without Pop-up Blockersoutli.txt 1.2 KB
System Changes To Foil Hackers And Browser Hijacke.txt 7.7 KB
System File Checker For Windows Xp.txt 2.3 KB
Tcpip A Mammoth Description, Short and easy-Everything U want to know.txt 51 KB
Testing Wattage Consumption Of Your Computer, Measuring your computer's wattage.txt 9.3 KB
The Antivirus Defense-in-Depth Guide.txt 2.8 KB
The difference between DVD-R, DVD+R, DVD+RW and DVD-RW.txt 3.7 KB
The Modern Phreakers Guide To Beige Boxing.txt 4.3 KB
The Modern Phreakers Guide To Payphones.txt 7 KB
The Port Guide, Port number and info.txt 24.6 KB
The Ultimate Guide To Installing Windows Xp Sp2.txt 3.1 KB
Three Ways Of Bypass Starforce Cd Protection.txt 2.5 KB
Tip for shutdown windows - virus.txt 397 Bytes
Tips And Tricks, Windows XP.txt 41.2 KB
Tired Of Reinstalling Windows.txt 2.3 KB
To Get And Show The Ip Via Javascript.txt 632 Bytes
Top 5 Myths About Safe Surfing, PC Magazine.txt 3.4 KB
Torrent_downloaded_from_Demonoid.com.txt 47 Bytes
Transferring Data.txt 6.4 KB
Translating Binary To Text.txt 6.2 KB
Translating Binary to Text2.txt 5.7 KB
Trojan Ports.txt 13.8 KB
Turn MSN Messenger Display Pix into User Pix on XP.txt 2.5 KB
Turn Off Unneeded Services, speed up pc.txt 1.6 KB
Tutorial Get the serial number you need.txt 899 Bytes
Tutorial How to create a bootable Windows XP SP1 CD (Nero).txt 2.2 KB
Tutorials - blacksun.box.sk / coding / Base Number Systems.html 7.8 KB
Tutorials - blacksun.box.sk / coding / BASIC C Socket Programming In Unix For Newbies.txt 21.5 KB
Tutorials - blacksun.box.sk / coding / Basics of am 3mp33j3w.txt 18.6 KB
Tutorials - blacksun.box.sk / coding / Batch File Programming.txt 41.7 KB
Tutorials - blacksun.box.sk / coding / BOOLEAN LOGIC GATES.html 14 KB
Tutorials - blacksun.box.sk / coding / C++ Tutorial By Clayman.html 23.8 KB
Tutorials - blacksun.box.sk / coding / Creating A Simple Hit Counter In PHP.html 8.8 KB
Tutorials - blacksun.box.sk / coding / Creating A Simple Search Engine In PHP.html 9.6 KB
Tutorials - blacksun.box.sk / coding / Creating Truly Skinnable Web Sites.html 13.6 KB
Tutorials - blacksun.box.sk / coding / Escape Quotes In Perl Shell.html 7.6 KB
Tutorials - blacksun.box.sk / coding / Flat databases in Perl.html 27.1 KB
Tutorials - blacksun.box.sk / coding / Introduction to Buffer Overflow.htm 37.6 KB
Tutorials - blacksun.box.sk / coding / Introduction to Perl.zip 31.4 KB
Tutorials - blacksun.box.sk / coding / IRC Bot In Perl.html 14.1 KB
Tutorials - blacksun.box.sk / coding / pascal.txt 70.1 KB
Tutorials - blacksun.box.sk / coding / Python for Newbies.htm 55 KB
Tutorials - blacksun.box.sk / coding / Sk00l m3 ASM!!#@$!@#.txt 112.8 KB
Tutorials - blacksun.box.sk / coding / The Boot Sector.html 19.3 KB
Tutorials - blacksun.box.sk / coding / The C Programming Language Torn Apart.html 24.5 KB
Tutorials - blacksun.box.sk / coding / The Perl Weekly Journal 1st edition.html 29.8 KB
Tutorials - blacksun.box.sk / coding / The Perl Weekly Journal 2nd edition.html 14.3 KB
Tutorials - blacksun.box.sk / coding / The Perl Weekly Journal 3rd edition.html 22.6 KB
Tutorials - blacksun.box.sk / coding / The Perl Weekly Journal 4th edition.html 18 KB
Tutorials - blacksun.box.sk / coding / Tutorial Assembly for nerds using linux - part 1.txt 7.7 KB
Tutorials - blacksun.box.sk / coding / Using Databases In PHP.html 11.7 KB
Tutorials - blacksun.box.sk / coding / Win32 Multithreading and Synchronization.html 24.9 KB
Tutorials - blacksun.box.sk / coding / WINDOWS INTERNET PROGRAMMING PART 3.html 69 KB
Tutorials - blacksun.box.sk / coding / WINDOWS INTERNET PROGRAMMING part1.html 112.6 KB
Tutorials - blacksun.box.sk / coding / WINDOWS INTERNET PROGRAMMING {part 2}.html 31.6 KB
Tutorials - blacksun.box.sk / encrypt / algorithms.html 189.1 KB
Tutorials - blacksun.box.sk / encrypt / base64.htm 94.6 KB
Tutorials - blacksun.box.sk / encrypt / desbreak.zip 4.9 KB
Tutorials - blacksun.box.sk / encrypt / encryption.txt 8.4 KB
Tutorials - blacksun.box.sk / encrypt / encryption_auth.html 15.2 KB
Tutorials - blacksun.box.sk / encrypt / passwd.txt 49.4 KB
Tutorials - blacksun.box.sk / encrypt / passwd2.html 74.7 KB
Tutorials - blacksun.box.sk / encrypt / pgp.html 20 KB
Tutorials - blacksun.box.sk / encrypt / quantum / Axes.jpg 5.7 KB
Tutorials - blacksun.box.sk / encrypt / quantum / CrptoProcess.jpg 21.3 KB
Tutorials - blacksun.box.sk / encrypt / quantum / Electro.jpg 18.9 KB
Tutorials - blacksun.box.sk / encrypt / quantum / NormalCrypto.jpg 17.1 KB
Tutorials - blacksun.box.sk / encrypt / quantum / NormalCryptoS.jpg 13.7 KB
Tutorials - blacksun.box.sk / encrypt / quantum / Phase.jpg 19.1 KB
Tutorials - blacksun.box.sk / encrypt / quantum / QuantumCrypto.jpg 13 KB
Tutorials - blacksun.box.sk / encrypt / quantum / QuantumCryptoS.jpg 16 KB
Tutorials - blacksun.box.sk / encrypt / quantum / quantum_cryptography.htm 34.9 KB
Tutorials - blacksun.box.sk / encrypt / quantum.zip 128.3 KB
Tutorials - blacksun.box.sk / encrypt / rsa.txt 10.5 KB
Tutorials - blacksun.box.sk / encrypt / ssl.html 8.5 KB
Tutorials - blacksun.box.sk / encrypt / ssltun.html 7.6 KB
Tutorials - blacksun.box.sk / hardware / buildcomp.html 12.2 KB
Tutorials - blacksun.box.sk / hardware / cdrom.html 9.1 KB
Tutorials - blacksun.box.sk / hardware / harddrive.html 7.5 KB
Tutorials - blacksun.box.sk / hardware / hardware.html 15.8 KB
Tutorials - blacksun.box.sk / hardware / memory.html 7.6 KB
Tutorials - blacksun.box.sk / hardware / overclocking.html 25.2 KB
Tutorials - blacksun.box.sk / hardware / PC_Hardware.html 19.5 KB
Tutorials - blacksun.box.sk / history / hod.html 41.5 KB
Tutorials - blacksun.box.sk / humor / flame.html 9.8 KB
Tutorials - blacksun.box.sk / humor / hackattack.html 3.9 KB
Tutorials - blacksun.box.sk / humor / jokerrap.html 2.3 KB
Tutorials - blacksun.box.sk / irc / eggdrops.html 41.8 KB
Tutorials - blacksun.box.sk / irc / fserv.html 48.3 KB
Tutorials - blacksun.box.sk / irc / ircwar.html 53.7 KB
Tutorials - blacksun.box.sk / lecture / cpplecture.html 18.6 KB
Tutorials - blacksun.box.sk / lecture / hacker.txt 11.2 KB
Tutorials - blacksun.box.sk / lecture / informatic.html 24.2 KB
Tutorials - blacksun.box.sk / lecture / irc2.html 141.2 KB
Tutorials - blacksun.box.sk / lecture / linuxnetworking.html 59.7 KB
Tutorials - blacksun.box.sk / lecture / LKMlecture.html 30.1 KB
Tutorials - blacksun.box.sk / lecture / mirclecture.html 24.4 KB
Tutorials - blacksun.box.sk / lecture / ntsec.html 70.2 KB
Tutorials - blacksun.box.sk / lecture / perlfilterlecture.html 39.1 KB
Tutorials - blacksun.box.sk / lecture / Perllecture.html 32.6 KB
Tutorials - blacksun.box.sk / lecture / phpl.html 33.6 KB
Tutorials - blacksun.box.sk / lecture / sqllecture.html 35 KB
Tutorials - blacksun.box.sk / lecture / traceroute.txt 5.1 KB
Tutorials - blacksun.box.sk / lecture / vpnlecture.html 91.1 KB
Tutorials - blacksun.box.sk / lecture / wardriving.html 21.2 KB
Tutorials - blacksun.box.sk / local / recover.txt 4.8 KB
Tutorials - blacksun.box.sk / local / standsec.html 44.1 KB
Tutorials - blacksun.box.sk / misc / beinghacker.html 43.9 KB
Tutorials - blacksun.box.sk / misc / ezine.txt 7.3 KB
Tutorials - blacksun.box.sk / misc / kiddies.txt 20.2 KB
Tutorials - blacksun.box.sk / misc / search2.txt 38.3 KB
Tutorials - blacksun.box.sk / misc / social.html 15.1 KB
Tutorials - blacksun.box.sk / net / adblock.html 12.7 KB
Tutorials - blacksun.box.sk / net / advisory01.html 25.6 KB
Tutorials - blacksun.box.sk / net / ankitgeo.htm 49 KB
Tutorials - blacksun.box.sk / net / ankit_smtp.htm 59.6 KB
Tutorials - blacksun.box.sk / net / cable.html 31.3 KB
Tutorials - blacksun.box.sk / net / cable.txt 20.9 KB
Tutorials - blacksun.box.sk / net / caching.html 11.9 KB
Tutorials - blacksun.box.sk / net / close.html 34 KB
Tutorials - blacksun.box.sk / net / Default Passwords.html 1.1 MB
Tutorials - blacksun.box.sk / net / Exploiting Cisco Systems.txt 20.5 KB
Tutorials - blacksun.box.sk / net / Exploiting File and Print Sharing.html 28.5 KB
Tutorials - blacksun.box.sk / net / Exploits Explained II The #2,000 bug.txt 4.3 KB
Tutorials - blacksun.box.sk / net / firewalls_torn.html 13.2 KB
Tutorials - blacksun.box.sk / net / ftp.html 11.7 KB
Tutorials - blacksun.box.sk / net / HACKER BEING - on the meaning of being a hacker.html 43.9 KB
Tutorials - blacksun.box.sk / net / Hacking CGI - Security and Exploitation.html 108.2 KB
Tutorials - blacksun.box.sk / net / http.txt 20 KB
Tutorials - blacksun.box.sk / net / icq.txt 52.9 KB
Tutorials - blacksun.box.sk / net / info.html 5.5 KB
Tutorials - blacksun.box.sk / net / inputval.txt 6.2 KB
Tutorials - blacksun.box.sk / net / Internetarch.html 28.2 KB
Tutorials - blacksun.box.sk / net / INTRODUCTION TO DENIAL OF SERVICE.txt 46.2 KB
Tutorials - blacksun.box.sk / net / IP and port Info using Netstat.txt 10.5 KB
Tutorials - blacksun.box.sk / net / ip.html 8.9 KB
Tutorials - blacksun.box.sk / net / kerberos.html 35.8 KB
Tutorials - blacksun.box.sk / net / lecture1.html 35 KB
Tutorials - blacksun.box.sk / net / Mail Bombing and List Linking.txt 7.3 KB
Tutorials - blacksun.box.sk / net / MailMachine flaws.txt 4.9 KB
Tutorials - blacksun.box.sk / net / masquerading.html 11.8 KB
Tutorials - blacksun.box.sk / net / mlist.txt 9.6 KB
Tutorials - blacksun.box.sk / net / net_toolz.html 76.5 KB
Tutorials - blacksun.box.sk / net / osmod1.02.htm 21.4 KB
Tutorials - blacksun.box.sk / net / pop3.html 8.4 KB
Tutorials - blacksun.box.sk / net / proxy.html 12.2 KB
Tutorials - blacksun.box.sk / net / rmhacking.html 16.2 KB
Tutorials - blacksun.box.sk / net / sendmail.html 81.7 KB
Tutorials - blacksun.box.sk / net / sendmail2.txt 78.3 KB
Tutorials - blacksun.box.sk / net / sigscr101.html 15.7 KB
Tutorials - blacksun.box.sk / net / tcpip.html 30.8 KB
Tutorials - blacksun.box.sk / net / trojans.html 13.2 KB
Tutorials - blacksun.box.sk / net / unixvirii.txt 11.2 KB
Tutorials - blacksun.box.sk / net / usenet.html 21.3 KB
Tutorials - blacksun.box.sk / novell / Novell Hacking for Complete Newbies.html 31.1 KB
Tutorials - blacksun.box.sk / novell / Novell Netware - Cracking Netware.htm 53.1 KB
Tutorials - blacksun.box.sk / tools / Cracking Unix password files for beginners.html 22.2 KB
Tutorials - blacksun.box.sk / tools / How to use the Fast Zip Cracker (FZC).html 11.7 KB
Tutorials - blacksun.box.sk / unix / 2038-time-bug.txt 7.1 KB
Tutorials - blacksun.box.sk / unix / etc.html 12.5 KB
Tutorials - blacksun.box.sk / unix / linux.html 35 KB
Tutorials - blacksun.box.sk / unix / linuxgames.html 5.8 KB
Tutorials - blacksun.box.sk / unix / linuxhdtweak.html 6.4 KB
Tutorials - blacksun.box.sk / unix / linuxnet.txt 34.7 KB
Tutorials - blacksun.box.sk / unix / shell.html 18.3 KB
Tutorials - blacksun.box.sk / unix / slackcs.txt 7 KB
Tutorials - blacksun.box.sk / unix / tcpwrappers.html 18.8 KB
Tutorials - blacksun.box.sk / unix / unixsec.html 59 KB
Tutorials - blacksun.box.sk / unix / winmodem.html 3.9 KB
Tutorials - blacksun.box.sk / win / debug.html 15.7 KB
Tutorials - blacksun.box.sk / win / foolproof.html 8.4 KB
Tutorials - blacksun.box.sk / win / foolproof2.html 10.3 KB
Tutorials - blacksun.box.sk / win / ipc.html 4.9 KB
Tutorials - blacksun.box.sk / win / reg.html 10.3 KB
Tutorials - blacksun.box.sk / win / registry.html 22.2 KB
Tutorials - blacksun.box.sk / win / win2kinstall.html 11.5 KB
Tutorials - blacksun.box.sk / win / windos9x.zip 11.6 KB
Tutorials - blacksun.box.sk / win / windows.html 25.7 KB
Tutorials - blacksun.box.sk / win / winerror.html 8.6 KB
Tutorials - blacksun.box.sk / win / winsecret.html 39.8 KB
Tutorials - blacksun.box.sk / win / winsecurity2.html 56.4 KB
Ultimate Google Way.txt 803 Bytes
ULTIMATE GUIDE TO BYPASS BIOS PASSWORDS!.txt 9 KB
Uninstall Windows Xp And Return To My Old Windows.txt 1.1 KB
Uninstalling Norton 2004 Products.txt 888 Bytes
Unlimited Rapidshare Downloads.txt 842 Bytes
Untold Window Tips.txt 34.6 KB
Untold Windows Secrets.txt 35.6 KB
Untold Windows Tips.txt 34.4 KB
Unused space on hard drives recovered.txt 5.6 KB
Use Hotkeys To Switch Programs.txt 496 Bytes
Useful Download Guide, Fix Down, 0daycn Ttdown, Links.txt 8.1 KB
User's Guide To Avoiding Virus Infections, Keeping an eye out for viruses.txt 10.2 KB
Using Google As A Calculator, A Tutorial.txt 2.9 KB
Using Google for searching ebooks.txt 691 Bytes
Using Rapid Share, How to use them and skip the BS.txt 2.8 KB
Video Avatars.txt 862 Bytes
Viewing Leftover Driver Entries.txt 1.6 KB
Virtual Memory Information.txt 6.7 KB
Virtual Memory Optimization Guide Rev. 4.0 - Final.txt 81.9 KB
Want To Download Torrent File By Using Google.txt 202 Bytes
Warez Definations.txt 19.7 KB
WAREZ DEFINITION.txt 18.7 KB
Way To Download From Brturbo, FireFox.txt 486 Bytes
We Don't Need No Education, Online classes made easy.txt 2.3 KB
Welcome to The king's meaning's of how to kick some-one's ASS!.txt 4.4 KB
What is the Registry.txt 13.2 KB
What Should I Do With Image Files.txt 3.2 KB
What You Wanted To Know About Movie Jargon, But Were Afraid To Ask.txt 17.3 KB
When Good Discs Go Bad.txt 10.5 KB
Where Is Winipcfg In Winxp.txt 632 Bytes
Who's Seeding The Net With Spyware.txt 5.3 KB
Why wait 35 Seconds at eZshare.txt 1.6 KB
Win 2000 Dr. Watsson.txt 237 Bytes
Windows 2000 Tips & Tricks.txt 4.6 KB
Windows 2003 System Restore, How to activate system restore in W2K3.txt 5.5 KB
Windows Scan Count Down Time.txt 556 Bytes
Windows Shortcuts.txt 12.8 KB
WINDOWS TRUE HIDDEN FILES.txt 9.5 KB
Windows Tweak,
Hack Your Start Button.txt 3.3 KB
Windows Xp - Speed Up Your Network and Internet Access.txt 2.7 KB
WINDOWS XP HIDDEN APPS.txt 2.6 KB
Windows XP Registry Tweaks.txt 34.1 KB
Windows XP Startup and Performance Tweaks.txt 1.8 KB
Windows Xp Tips 'n' Tricks.txt 28.5 KB
Windows Xp Tweaks, A work in progress.txt 3 KB
Windows XP Tweaks.txt 2.4 KB
WinRar Tutorial - Compression profiles, passwords and more.txt 5.8 KB
Winsock 2 Repair.txt 2.1 KB
WinXP 3 Tips.txt 1.9 KB
Winxp Application Defrag, faster access for used programs.txt 309 Bytes
Winxp Applications Startup Time, Decrease your Applications startup time.txt 1.2 KB
WinXP Bootable CD.txt 2.2 KB
Winxp System Response, reboot whitout rebooting.txt 625 Bytes
Winxp Tips And Tricks, Winsock 2 repair.txt 2.2 KB
Xp Auto Install.txt 1.8 KB
Xp Folder View Does Not Stay To You're Setting., Grab your registry editor and join in.txt 1.9 KB
XP REPAIR INSTALL.txt 5.9 KB
XP Tweaking.txt 15.7 KB
Yahoo + geocities Posts.txt 3.1 KB
Yahoo Messeger, no ad's.txt 852 Bytes
You Want Lots Of Music, Appz, Anything, Try Dex Hunting.txt 1.5 KB
Your Home Page Nevr Being Changed.txt 516 Bytes
Your Own Home Server - Introduction.txt 11.2 KB
[php] Navigations.txt 1.3 KB
Download Link
http://rapidshare.com/files/131640618/1000_Tutorials.rar